* feat(mcp): workspace container with bridge architecture
Migrate MCP containers to use UDS-based bridge communication instead of
TCP gRPC. Containers now mount runtime binaries and Unix domain sockets
from the host, eliminating the need for a dedicated MCP Docker image.
- Remove Dockerfile.mcp and entrypoint.sh in favor of standard base images
- Add toolkit Dockerfile for building MCP binary separately
- Containers use bind mounts for /opt/memoh (runtime) and /run/memoh (UDS)
- Update all config files with new runtime_path and socket_dir settings
- Support custom base images per bot (debian, alpine, ubuntu, etc.)
- Legacy container detection and TCP fallback for pre-bridge containers
- Frontend: add base image selector in container creation UI
* feat(container): SSE progress bar for container creation
Add real-time progress feedback during container image pull and creation
using Server-Sent Events, without breaking the existing synchronous JSON
API (content negotiation via Accept header).
Backend:
- Add PullProgress/LayerStatus types and OnProgress callback to
PullImageOptions (containerd service layer)
- DefaultService.PullImage polls ContentStore.ListStatuses every 500ms
when OnProgress is set; AppleService ignores it
- CreateContainer handler checks Accept: text/event-stream and switches
to SSE branch: pulling → pull_progress → creating → complete/error
Frontend:
- handleCreateContainer/handleRecreateContainer use fetch + SSE instead
of the SDK's synchronous postBotsByBotIdContainer
- Progress bar shows layer-level pull progress (offset/total) during
pulling phase and indeterminate animation during creating phase
- i18n keys added for pullingImage and creatingContainer (en/zh)
* fix(container): clear stale legacy route and type create SSE
* fix(ci): resolve lint errors and arm64 musl node.js download
- Fix unused-receiver lint: rename `s` to `_` on stub methods in
manager_legacy_test.go
- Fix sloglint: use slog.DiscardHandler instead of
slog.NewTextHandler(io.Discard, nil)
- Handle missing arm64 musl Node.js builds: unofficial-builds.nodejs.org
does not provide arm64 musl binaries, fall back to glibc build
* fix(lint): address errcheck, staticcheck, and gosec findings
- Discard os.Setenv/os.Remove return values explicitly with _
- Use omitted receiver name instead of _ (staticcheck ST1006)
- Tighten directory permissions from 0o755 to 0o750 (gosec G301)
* fix(lint): sanitize socket path to satisfy gosec G703
filepath.Clean the env-sourced socket path before os.Remove
to avoid path-traversal taint warning.
* fix(lint): use nolint directive for gosec G703 on socket path
filepath.Clean does not satisfy gosec's taint analysis. The socket
path comes from MCP_SOCKET_PATH env (operator-configured) or a
compiled-in default, not from end-user input.
* refactor: rename MCP container/bridge to workspace/bridge
Split internal/mcp/ to separate container lifecycle management from
Model Context Protocol connections, eliminating naming confusion:
- internal/mcp/ (container mgmt) → internal/workspace/
- internal/mcp/mcpclient/ → internal/workspace/bridge/
- internal/mcp/mcpcontainer/ → internal/workspace/bridgepb/
- cmd/mcp/ → cmd/bridge/
- config: MCPConfig → WorkspaceConfig, [mcp] → [workspace]
- container prefix: mcp-{id} → workspace-{id}
- labels: mcp.bot_id → memoh.bot_id, add memoh.workspace=v1
- socket: mcp.sock → bridge.sock, env BRIDGE_SOCKET_PATH
- runtime: /opt/memoh/runtime/mcp → /opt/memoh/runtime/bridge
- devenv: mcp-build.sh → bridge-build.sh
Legacy containers (mcp- prefix) detected by container name prefix
and handled via existing fallback path.
* fix(container): use memoh.workspace=v3 label value
* refactor(container): drop LegacyBotLabelKey, infer bot ID from container name
Legacy containers use mcp-{botID} naming, so bot ID can be derived
via TrimPrefix instead of looking up the mcp.bot_id label.
* fix(workspace): resolve containers via manager and drop gateway container ID
* docs: fix stale mcp references in AGENTS.md and DEPLOYMENT.md
* refactor(workspace): move container lifecycle ownership into manager
* dev: isolate local devenv from prod config
* toolkit: support musl node runtime
* containerd: fix fallback resolv.conf permissions
* web: preserve container create progress on completion
* web: add bot creation wait hint
* fix(workspace): preserve image selection across recreate
* feat(web): shorten default docker hub image refs
* fix(container): address code review findings
- Remove synchronous CreateContainer path (SSE-only now)
- Move flusher check before WriteHeader to avoid committed 200 on error
- Fix legacy container IP not cached via ensureContainerAndTask path
- Add atomic guard to prevent stale pull_progress after PullImage returns
- Defensive copy for tzEnv slice to avoid mutating shared backing array
- Restore network failure severity in restartContainer (return + Error)
- Extract duplicate progress bar into ContainerCreateProgress component
- Fix codesync comments to use repo-relative paths
- Add SaaS image validation note and kernel version comment on reaper
* refactor(devenv): extract toolkit install into shared script
Unify the Node.js + uv download logic into docker/toolkit/install.sh,
used by the production Dockerfile and runnable locally for dev.
Dev environment no longer bakes toolkit into the Docker image — it is
volume-mounted from .toolkit/ instead, so wrapper script changes take
effect immediately without rebuilding. The entrypoint checks for the
toolkit directory and prints a clear error if missing.
* fix(ci): address go ci failures
* chore(docker): remove unused containerd image
* refactor(config): rename workspace image key
* fix(workspace): fix legacy container data loss on migration and stop swallowing errors
Three root causes were identified and fixed:
1. Delete() used hardcoded "workspace-" prefix to look up legacy "mcp-"
containers, causing GetContainer to return NotFound. CleanupBotContainer
then silently skipped the error and deleted the DB record without ever
calling PreserveData. Fix: resolve the actual container ID via
ContainerID() (DB → label → scan) before operating.
2. Multiple restore error paths were silently swallowed (logged as Warn
but not returned), so the user saw HTTP 200/204 with no data and no
error. Fix: all errors in the preserve/restore chain now block the
workflow and propagate to the caller.
3. tarGzDir used cached DirEntry.Info() for tar header size, which on
overlayfs can differ from the actual file size, causing "archive/tar:
write too long". Fix: open the file first, Fstat the fd for a
race-free size, and use LimitReader as a safeguard.
Also adds a "restoring" SSE phase so the frontend shows a progress
indicator ("Restoring data, this may take a while...") during data
migration on container recreation.
* refactor(workspace): single-point container ID resolution
Replace the `containerID func(string) string` field with a single
`resolveContainerID(ctx, botID)` method that resolves the actual
container ID via DB → label → scan → fallback. All ~16 lookup
callsites across manager.go, dataio.go, versioning.go, and
manager_lifecycle.go now go through this single resolver, which
correctly handles both legacy "mcp-" and new "workspace-" containers.
Only `ensureBotWithImage` inlines `ContainerPrefix + botID` for
creating brand-new containers — every other path resolves dynamically.
* fix(web): show progress during data backup phase of container recreate
The recreate flow (delete with preserve_data + create with restore_data)
blocked on the DELETE call while backing up /data with no progress
indication. Add a 'preserving' phase to the progress component so
users see "正在备份数据..." instead of an unexplained hang.
* chore: remove [MYDEBUG] debug logging
Clean up all 112 temporary debug log statements added during the
legacy container migration investigation. Kept only meaningful
warn-level logs for non-fatal errors (network teardown, rename
failures).

Memoh
Multi-Member, Structured Long-Memory, Containerized AI Agent System.
📌 Introduction to Memoh - The Case for an Always-On, Containerized Home Agent
Memoh is an always-on, containerized AI agent system. Create multiple AI bots, each running in its own isolated container with persistent memory, and interact with them across Telegram, Discord, Lark (Feishu), Email, or the built-in Web/CLI. Bots can execute commands, edit files, browse the web, call external tools via MCP, and remember everything — like giving each bot its own computer and brain.
Quick Start
One-click install (requires Docker):
curl -fsSL https://memoh.sh | sudo sh
Silent install with all defaults: curl -fsSL ... | sudo sh -s -- -y
Or manually:
git clone --depth 1 https://github.com/memohai/Memoh.git
cd Memoh
cp conf/app.docker.toml config.toml
# Edit config.toml
sudo docker compose up -d
Install a specific version:
curl -fsSL https://memoh.sh | sudo MEMOH_VERSION=v1.0.0 shUse CN mirror for slow image pulls:
curl -fsSL https://memoh.sh | sudo USE_CN_MIRROR=true shOn macOS or if your user is in the
dockergroup,sudois not required.
Visit http://localhost:8082 after startup. Default login: admin / admin123
See DEPLOYMENT.md for custom configuration and production setup.
Why Memoh?
OpenClaw is impressive, but it has notable drawbacks: stability issues, security concerns, cumbersome configuration, and high token costs. If you're looking for a stable, secure solution, consider Memoh.
Memoh is a multi-bot agent service built with Golang. It offers full graphical configuration for bots, Channels, MCP, and Skills. We use Containerd to provide container-level isolation for each bot and draw heavily from OpenClaw's Agent design.
Memoh Bot can distinguish and remember requests from multiple humans and bots, working seamlessly in any group chat. You can use Memoh to build bot teams, or set up accounts for family members to manage daily household tasks with bots.
Features
- 🤖 Multi-Bot Management: Create multiple bots; humans and bots, or bots with each other, can chat privately, in groups, or collaborate. Supports role-based access control (owner / admin / member) with ownership transfer.
- 👥 Multi-User & Identity Recognition: Bots can distinguish individual users in group chats, remember each person's context separately, and send direct messages to specific users. Cross-platform identity binding unifies the same person across Telegram, Discord, Lark, and Web.
- 📦 Containerized: Each bot runs in its own isolated containerd container. Bots can freely execute commands, edit files, and access the network within their containers — like having their own computer. Supports container snapshots for save/restore.
- 🧠 Memory Engineering: Multi-provider memory architecture — Built-in (off / sparse / dense modes), Mem0, and OpenViking. LLM-driven fact extraction, hybrid retrieval (dense semantic search + BM25 keyword + neural sparse vectors), 24-hour context loading, memory compaction & rebuild, and multi-language auto-detection.
- 💬 Multi-Platform: Supports Telegram, Discord, Lark (Feishu), Email, and built-in Web/CLI. Unified message format with rich text, media attachments, reactions, and streaming across all platforms. Cross-platform identity binding.
- 📧 Email: Multi-adapter email service (Mailgun, generic SMTP) with per-bot binding and outbound audit log. Bots can send and receive emails as a channel.
- 🔧 MCP (Model Context Protocol): Full MCP support (HTTP / SSE / Stdio). Built-in tools for container operations, memory search, web search, scheduling, messaging, and more. Connect external MCP servers for extensibility.
- 🧩 Subagents: Create specialized sub-agents per bot with independent context and skills, enabling multi-agent collaboration.
- 🎭 Skills & Identity: Define bot personality via IDENTITY.md, SOUL.md, and modular skill files that bots can enable/disable at runtime.
- 🌐 Browser: Each bot can have its own headless Chromium browser (via Playwright). Navigate pages, click elements, fill forms, take screenshots (with annotated element labels), read accessibility trees, manage tabs, and more — enabling real web automation and AI-driven browsing.
- 🔍 Web Search: 12 built-in search providers — Brave, Bing, Google, Tavily, DuckDuckGo, SearXNG, Serper, Sogou, Jina, Exa, Bocha, and Yandex — for web search and URL content fetching.
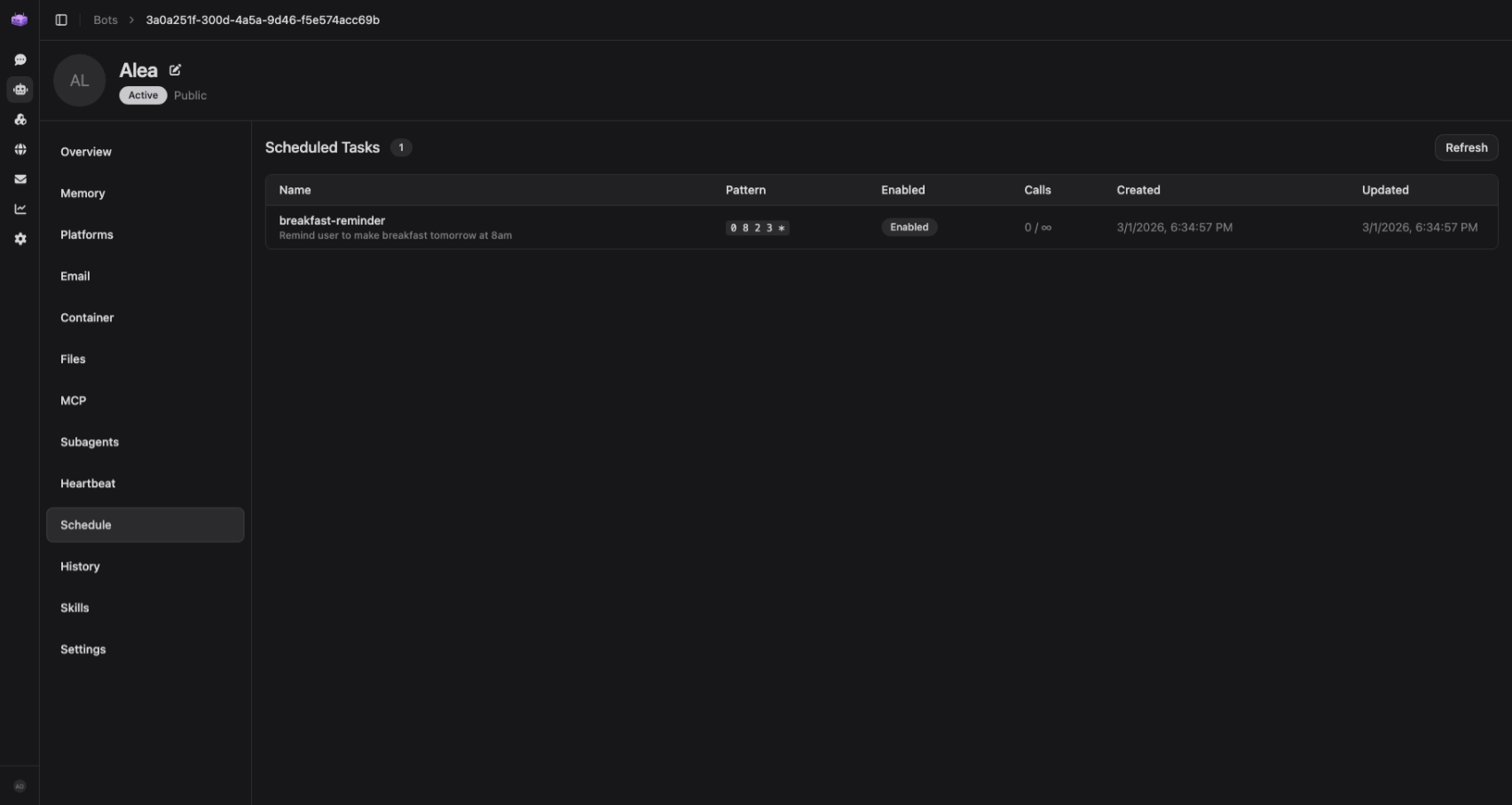
- ⏰ Scheduled Tasks: Cron-based scheduling with max-call limits. Bots can autonomously run commands or tools at specified intervals.
- 💓 Heartbeat: Periodic autonomous tasks — bots can perform routine operations (e.g., check-ins, summaries, monitoring) at configurable intervals with execution logging.
- 📥 Inbox: Cross-channel inbox — messages from other channels are queued and surfaced in the system prompt so the bot never misses context.
- 📊 Token Usage Tracking: Monitor token consumption per bot with usage statistics and visualization.
- 🧪 Multi-Model: Works with any OpenAI-compatible, Anthropic, or Google Generative AI provider. Per-bot model assignment for chat, memory, and embedding.
- 🖥️ Web UI: Modern dashboard (Vue 3 + Tailwind CSS) with real-time streaming chat, tool call visualization, in-chat file manager, container filesystem browser, and visual configuration for all settings. Dark/light theme, i18n.
- 🚀 One-Click Deploy: Docker Compose with automatic migration, containerd setup, and CNI networking. Interactive install script included.
Memory System
Memoh's memory system is built around Memory Providers — pluggable backends that control how a bot stores, retrieves, and manages long-term memory.
| Provider | Description |
|---|---|
| Built-in | Self-hosted, ships with Memoh. Three modes: Off (file-based, no vector search), Sparse (neural sparse vectors via local model, no API cost), Dense (embedding-based semantic search via Qdrant). |
| Mem0 | SaaS memory via the Mem0 API. |
| OpenViking | Self-hosted or SaaS memory with its own API. |
Each bot binds one provider. During chat, the bot automatically extracts key facts from every conversation turn and stores them as structured memories. On each new message, the most relevant memories are retrieved via hybrid search and injected into the bot's context — giving it personalized, long-term recall across conversations.
Additional capabilities include memory compaction (merge redundant entries), rebuild, manual creation/editing, and vector manifold visualization (Top-K distribution & CDF curves). See the documentation for setup details.
Gallery
 |
 |
 |
| Chat with Bots | Container & Bot Management | Provider & Model Configuration |
 |
 |
 |
| Container File Manager | Scheduled Tasks | Token Usage Tracking |
Tech Stack
| Layer | Stack |
|---|---|
| Backend | Go, Echo, sqlc, Uber FX, pgx/v5, containerd v2 |
| Agent Gateway | Bun, Elysia |
| Browser Gateway | Bun, Elysia, Playwright (Chromium) |
| Frontend | Vue 3, Vite, Pinia, Tailwind CSS, Reka UI |
| Storage | PostgreSQL, Qdrant |
| Infra | Docker, containerd, CNI |
| Tooling | mise, pnpm, swaggo, sqlc |
Architecture
┌──────────────────┐ ┌─────────────────┐ ┌──────────────┐
│ Channels │ │ Web UI │ │ CLI │
│ (TG/DC/FS/Email) │ │ (Vue 3 :8082) │ │ │
└────────┬─────────┘ └────────┬────────┘ └──────┬───────┘
│ │ │
▼ ▼ ▼
┌──────────────────────────────────────────────────────────┐
│ Server (Go :8080) │
│ Auth · Bots · Channels · Memory · Containers · MCP │
└──────────────────────┬───────────────────────────────────┘
│
┌───────────┼───────────┬───────────┐
▼ ▼ ▼ ▼
┌──────────┐ ┌─────────┐ ┌──────────────────┐ ┌───────────────────┐
│ PostgreSQL│ │ Qdrant │ │ Agent Gateway │ │ Browser Gateway │
│ │ │ (Vector)│ │ (Bun/Elysia :8081)│ │ (Playwright :8083) │
└──────────┘ └─────────┘ └────────┬──────────┘ └───────────────────┘
│
┌───────┼───────┐
▼ ▼ ▼
┌─────┐ ┌─────┐ ┌─────┐
│Bot A│ │Bot B│ │Bot C│ ← containerd
└─────┘ └─────┘ └─────┘
Roadmap
Please refer to the Roadmap for more details.
Development
Refer to CONTRIBUTING.md for development setup.
Star History
Contributors
LICENSE: AGPLv3
Copyright (C) 2026 Memoh. All rights reserved.





